The recent Department of Justice operation against a Russian-controlled botnet represents a shift from passive defense to proactive infrastructure degradation. By targeting the Domain Name System (DNS) hijacking capabilities of the GRU-affiliated group known as APT28 (or Fancy Bear), the U.S. government executed a surgical strike against the fundamental mechanics of state-sponsored cyber espionage. This operation did not merely delete malware; it dismantled a logistical supply chain designed to misdirect internet traffic at scale.
The Architecture of Interception
The GRU’s strategy relied on a specific technical vulnerability: the exploitation of outdated and poorly secured Small Office/Home Office (SOHO) routers. These devices served as the foundational layer for a sophisticated DNS hijacking network. To understand the impact, one must map the three functional layers of this operation:
- The Persistence Layer: Compromised SOHO routers provided a distributed, global footprint that is difficult to blacklist. Because these IPs belong to residential or small business accounts, they carry a high "reputation score" compared to known data center IPs, allowing malicious traffic to blend into legitimate background noise.
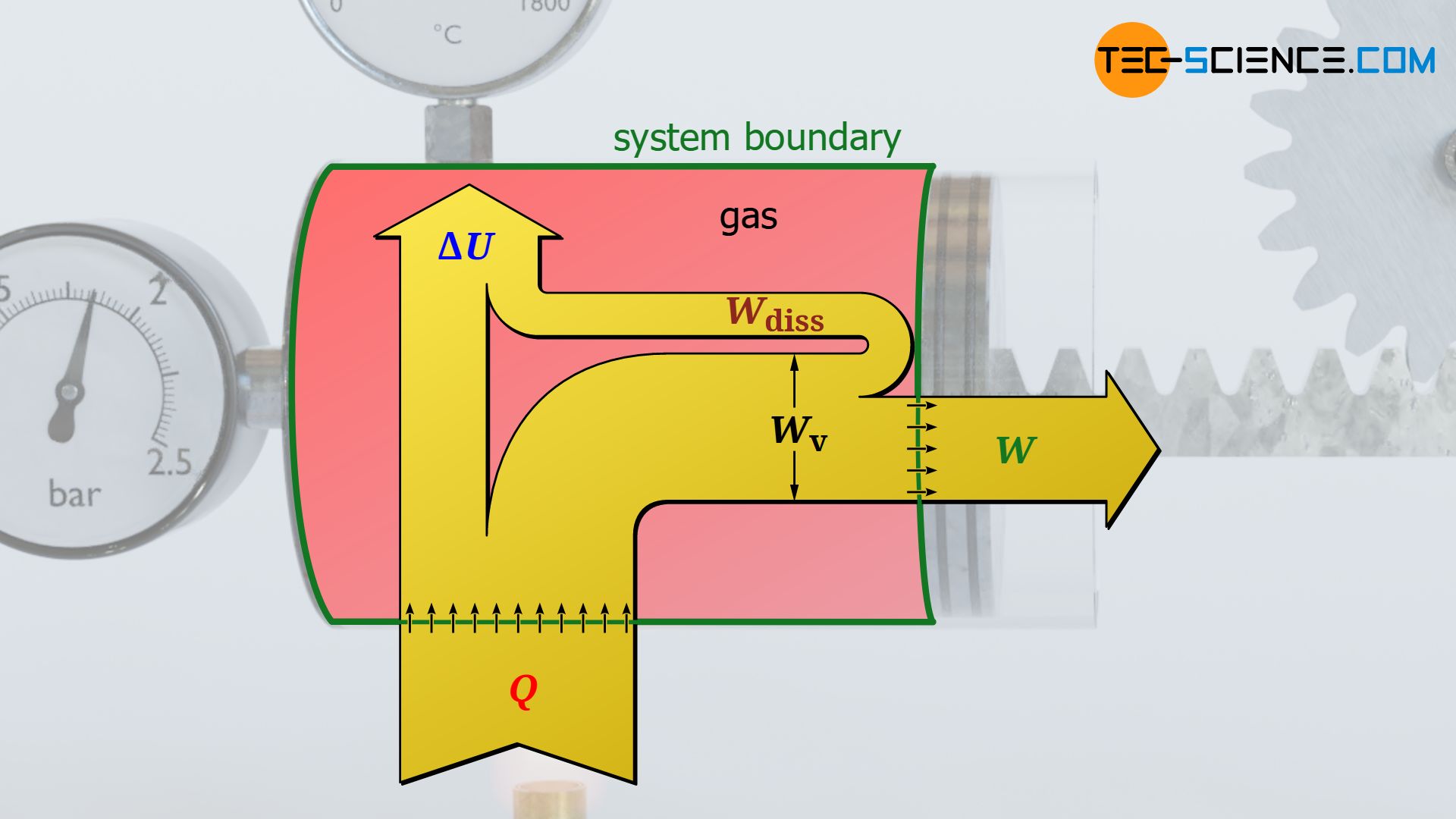
- The Redirection Layer: By gaining administrative control over these routers, APT28 modified their DNS settings. DNS acts as the phonebook of the internet; by altering it, the attackers could silently reroute a user’s request for a legitimate site—such as a government portal or a secure email provider—to a malicious server under GRU control.
- The Harvesting Layer: Once the traffic reached the attacker-controlled server, the "Man-in-the-Middle" (MitM) attack was completed. This allowed for the interception of credentials, session cookies, and sensitive data before passing the user back to the actual site to avoid detection.
Deconstructing the Moobot Botnet
The specific instrument in this engagement was the "Moobot" botnet. Unlike general-purpose malware designed for cryptocurrency mining or DDoS attacks, Moobot was repurposed by the GRU as a specialized proxy network. The technical sophistication lies not in the malware itself—which is a variant of the well-known Mirai code—but in its operational integration into the Russian military's intelligence-gathering apparatus.
The botnet functioned as a "clean" relay system. When a GRU operative initiated a cyberattack, they did not connect directly to the target. Instead, they tunneled their traffic through the Moobot network. This created a dual-layered obfuscation:
- Geographic Misdirection: An attack originating in Moscow could appear to come from a compromised router in suburban Ohio.
- Protocol Camouflage: Because the traffic passed through residential hardware, it followed the behavioral patterns of standard web browsing, bypassing many automated anomaly detection systems.
The Cost Function of Cyber Counter-Offensives
Government intervention in private infrastructure is a high-stakes calculation. The Justice Department’s "disruption" involves a specific legal and technical sequence: obtaining search warrants to remotely access the compromised routers and issuing commands to delete the malware and close the vulnerability.
The effectiveness of this strategy is measured by the Recovery Cost for the Adversary. In cyber warfare, total elimination of an actor is impossible. Success is instead defined by forcing the opponent to expend more resources—time, money, and human capital—to rebuild their infrastructure than the defender spent to destroy it.
The U.S. operation achieved high-impact asymmetry through three levers:
- Irreparable Asset Loss: By scrubbing the routers and updating their firewall rules, the U.S. permanently removed those specific nodes from the GRU’s inventory.
- Intelligence Exposure: The process of dismantling the network required the U.S. to publicly detail the GRU's Tactics, Techniques, and Procedures (TTPs). This forces the GRU to develop entirely new codebases and infiltration methods, a process that can take months or years.
- Psychological Friction: Operating under the knowledge that your "secret" infrastructure is being monitored and mapped by a rival intelligence service creates a chilling effect on future operations, slowing the tempo of state-sponsored espionage.
Vulnerability Economics of the SOHO Market
The core reason this network existed is a market failure in the hardware industry. SOHO routers are built for low cost and ease of use, often at the expense of security. This creates a "Tragedy of the Commons" in cyberspace, where individual security lapses collectively empower a foreign military.
The lifecycle of these vulnerabilities follows a predictable decay:
- Zero-Day Discovery: Attackers find a flaw in a specific router firmware.
- Automated Exploitation: Scripts scan the entire IPv4 address space to find and infect vulnerable devices.
- Infrastructure Maturation: The infected nodes are organized into a Command and Control (C2) hierarchy.
- Operationalization: The botnet is rented out or utilized for state-level objectives.
The U.S. disruption focused on the fourth stage, but the structural risk remains in the first two. Until the cost of producing insecure hardware exceeds the profit margins for manufacturers, the supply of potential botnet nodes will remain infinite.
Geopolitical Signaling and the Doctrine of Persistent Engagement
This operation is a tangible application of the "Persistent Engagement" doctrine adopted by U.S. Cyber Command. This doctrine posits that to maintain a competitive advantage, a state must constantly interact with the adversary’s infrastructure, rather than waiting to respond to a specific crisis.
The message to the Kremlin is a shift in the "Rules of Engagement." Historically, cyber espionage was viewed as a gray-zone activity where the only consequence was the loss of the specific data being stolen. By physically reaching into the GRU's operational tools and breaking them, the U.S. is signaling that the infrastructure itself is now a legitimate target for counter-strikes.
Technical Limitations and Residual Risk
While the operation was successful in neutralizing the Moobot network, it is not a panacea. Several technical bottlenecks limit the long-term efficacy of such disruptions:
- The Re-Infection Cycle: If the underlying vulnerability in the router is not patched by the manufacturer or the user, the device remains susceptible to the next botnet that scans it. The DOJ can remove the "Russian" malware, but it cannot legally or practically assume the role of a permanent managed security provider for millions of private citizens.
- The Fragmentation of Command: APT28 is one of many units. The GRU and SVR (Russia's Foreign Intelligence Service) maintain redundant infrastructures. Disrupting one network might only shift traffic to another, albeit with a temporary loss in capacity.
- Shadow Infrastructure: Sophisticated actors are moving away from centralized botnets toward more ephemeral "serverless" or cloud-native architectures that do not rely on physical hardware like routers, making similar disruption operations significantly more complex.
The path forward requires a transition from reactive "cleanup" operations to a regime of Infrastructure Hardening. This includes the implementation of Secure-by-Design mandates for consumer electronics and the expansion of public-private partnerships that allow Internet Service Providers (ISPs) to automatically block traffic directed toward known C2 nodes.
The strategic priority is now the automation of the "Detect-to-Disrupt" cycle. The time between the GRU compromising a router and the U.S. government neutralizing it must be reduced from months to minutes. This requires a shift from legalistic, warrant-heavy responses to algorithmic defenses that can identify and isolate malicious DNS traffic patterns in real-time. Until this speed-of-light defense is realized, state actors will continue to find high-yield returns in the exploitation of the internet's fundamental protocols.
The immediate move for enterprise and government IT leaders is the mandatory adoption of DNS over HTTPS (DoH) or DNS over TLS (DoT). By encrypting DNS queries, the redirection layer used by APT28 is rendered ineffective, as the compromised router can no longer see, much less manipulate, the destination of the user's request. This effectively "blinds" the hijacking infrastructure and provides a scalable defense that does not rely on the physical security of edge devices.